I’m the Chief Operations Officer at Cobalt, a Pen Testing as a Service company that has performed over 5800 pentests to-date. It’s my job to make sure that each and every one of our pentest programs is up and running properly. A large part of that deals with preparing organizations and pentesters for the pentest engagement. If you know that you are going to be running a pentest, internal or external, then you need to get your ducks in a row and prepare for it.
Often times there is a negative connotation associated with pentesting preparation; that it’s this agonizing, irritating, and time-consuming task. However, this doesn’t have to be the case. Security professionals agree PtaaS reduced time-to-results by 50% compared to traditional consulting engagements.
These three tips will help make preparing for a pentest much easier:
1. Drop the Silos — Align security and development teams
To effectively find and fix application security issues there needs to be collaboration and communication between the security, product, and development teams. Organizations can use pentesting to facilitate this conversation. Pentest findings serve as a great feedback loop for this conversation, and it gives developers an opportunity to understand the real-world implications of writing insecure code.
However, security organizations often focus on defect discovery instead of focusing on process and cross-functional relationships that are required to get issues fixed. By involving and coordinating with dev teams in the beginning of the pentesting preparation process then they will be more committed to fix the issues found. Developers should have an understanding around what is happening. Security teams will get better responses from dev, and dev will not feel like they are getting pushed around from security.
Note to security teams: Remember to deliver the good news about securely built modules etc. — this creates positive reinforcement and a nice work climate.
If you prepare the teams and align them on what will be tested. You can better facilitate a more open and positive line of communication during the pentest.
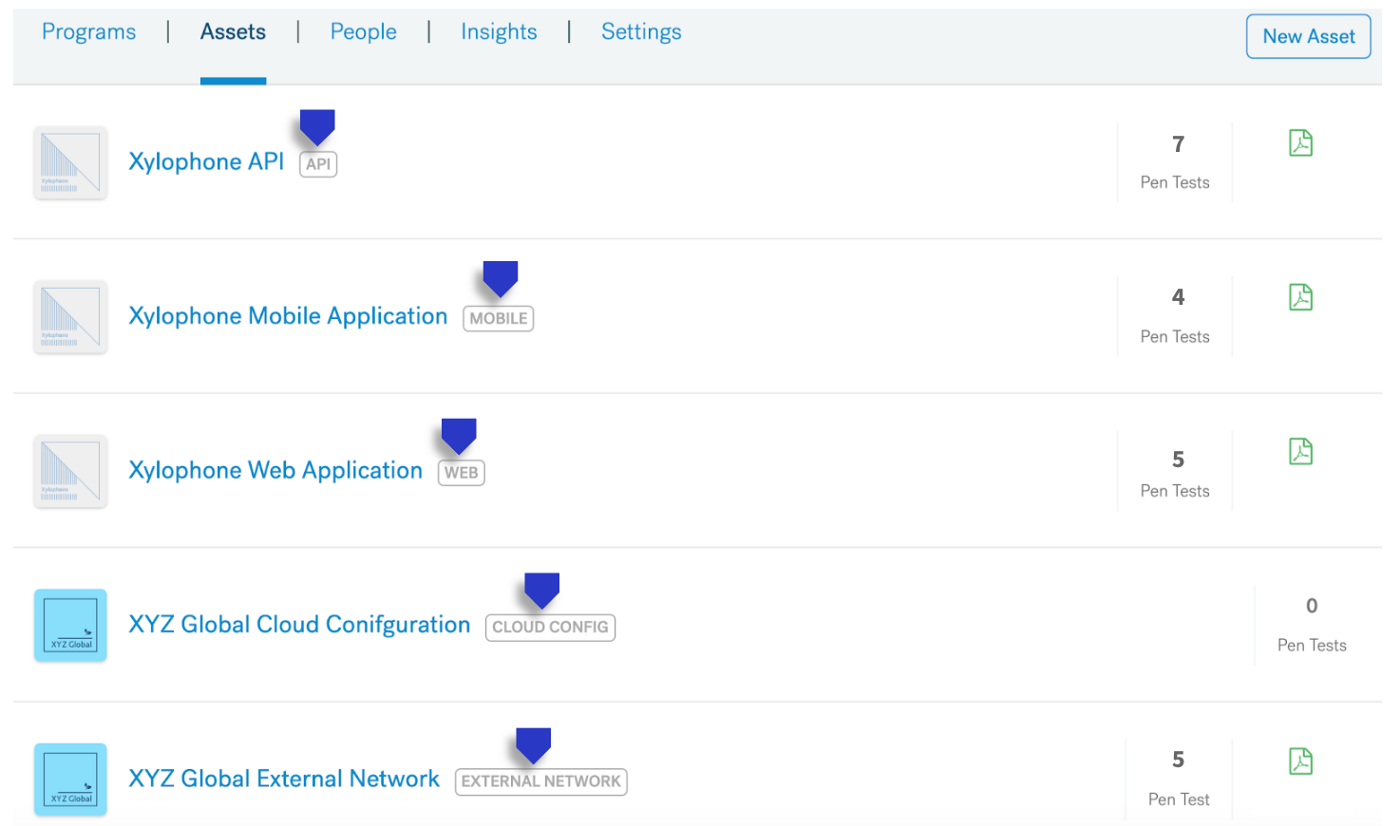
2. Focus on the Important — Clear and impactful scope
One common mistake with preparing for a pentest is that the security team feels that they need to provide the pentester with every single nitty-gritty detail about their application. Although including every detail can add a little value it is often a lot of unnecessary work. What is more important is to provide the tester with the critical workflows, key features, and data flows. Give them the important information, and that’s it. Too much information can make the important details get lost in the dust, as well as, take away from everyone’s valuable time.
The best way to think about it is, “what can I provide that gives the tester the information needed to perform the test, and that doesn’t take away too much of my/his/her time.” Maybe that is creating a short screen sharing video of common workflows, or providing a checklist of key features. That is up to you to decide, but just remember it’s not about just about quantity, quality plays a larger role.
3. Work with Experts — Obtain the right pentesters
It’s a no-brainer that you want to have highly skilled and qualified pentesters looking into your application, but it’s also just as important to have those tester’s skills match the scope of what you want tested. Skills matching is a critical component to achieving quality results in any penetration test. The benefit of a pentest shouldn’t just be in discovering vulnerabilities, but using that knowledge to reduce the risk associated with the application. The more important attributes of any penetration tester are skill set, experience, and performance. When choosing your testers, this could be internally or externally with pentest providers, you need match their skills to your tech stack. You want the tester to be familiar with what they are testing.
If you have the right workflows set in place, preparing for a pentest can be easy. Know what you’re testing, communicate this to the right teams, and have the best individuals, given your scope, perform the testing.
Hope these tips offer some guidance in preparing your pentest program. This blog was the first in a series about the pentesting process. Look out for the next blog post in this series that will dive into tips for kicking off your pentest.