Traditional pentesting still raises numerous operational challenges for agile and fast-paced companies. We surveyed 165 attendees of our live demos to learn more about their biggest pain points. Three stood out:
- 66% said pentesting is expensive and hard to do continuously;
- 57% cited difficulties with finding the right talent;
- 42% complained of long lead times to starting a pentest;
In fact, two-thirds said it took them 2-3 weeks to schedule and launch a pentest. And if that doesn’t break your SDLC, 73% said they sent vulnerability findings manually to their engineers, instead of having an automated workflow to instantly flag issues.
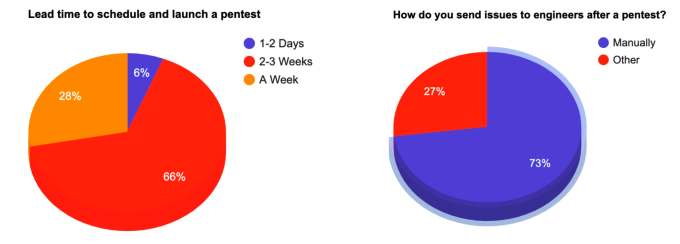
These stats capture the reasons why we do what we do. In a world where DevOps is taking hold and everything is shifting left, there is now a growing need more than ever to make pentesting as frictionless as possible. With Pentest as a Service, Cobalt combines a SaaS approach with a collaborative platform to help spin up pentests in days, not weeks, and transform pentesting into an efficient, integrated, and collaborative process.
But how exactly does it work? And does it work well?
To answer these questions, we invited SANS analyst Matt Bromiley to test our platform and share his observations on the overall pentesting experience. Matt is a SANS digital forensics and incident response instructor, teaching FOR508 (Advanced Incident Response, Threat Hunting, and Digital Forensics) and FOR572 (Advanced Network Forensics: Threat Hunting, Analysis, and Incident Response). He is a principal consultant at a global incident response and forensic analysis company, combining his experience in digital forensics, log analytics, and incident response and management.
Matt opted for a pentest on a Linux virtual machine in Microsoft Azure and recorded feedback on each step of the engagement: from setup and scoping, to how pentesters worked with his security team and delivered findings, rounding off with the structure of the final report, remediation assistance and retesting.
He describes the process in his latest report “Pentest as a Service with Cobalt”, sharing observations on the following questions:
Setup:
- How can I scope my pentest in a Pentest as a Service platform?
- How can I describe in-scope assets, objectives and special instructions?
Scheduling:
- How quickly can I schedule a pentest via the platform?
- What happens when I request to start the pentest?
- How long does the test last?
Stakeholders:
- How will my team work with Cobalt? Who is involved in the process?
- How and when can my team communicate with the pentesters?
- Who manages pentest delivery, and how?
Finding delivery:
- How, when and where are findings shared?
- Are high-priority findings highlighted to my team?
- What level of detail is provided on proof of concept, criticality and suggested fixes?
- Can my team raise additional questions with the pentesters? How?
- Can we send findings straight to our issue tracking workflows?
Remediation & retesting:
- Can we request a retest after we patch a vulnerability? How?
- Is that included in the pricing?
Reporting & data:
- What kind of data do you share at the end of the pentest?
- Can we export findings and data insights into reports?
- What kind of report formats does the platform support?
To read Matt's observations on all of these questions and more, you can access the report on our website: