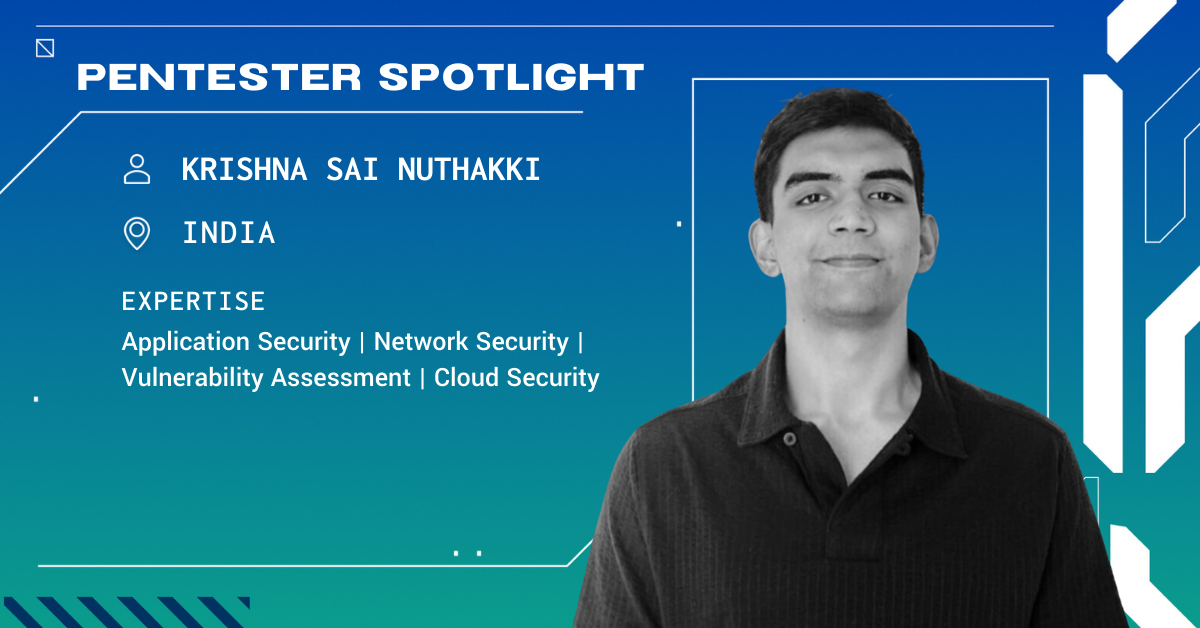
The Cobalt Pentester Spotlight highlights the fascinating journey of our Core members. Through an interview style, we share their experiences, background, and insights into the world of an accomplished pentester.
What's your handle? Do you use more than one? Where did it come from?
I go by Sunil45, and that’s the only handle I use. It’s simple and personal. Sunil is my name, and 45 comes from cricket. I’ve followed the game since childhood, and Rohit Sharma’s jersey number has always stood out to me. I admire his calmness and discipline under pressure, and over time, that number became something I connected with. So the handle just felt natural.
What got you into cybersecurity? How did you get into pentesting specifically?
My interest in cybersecurity began during my third year of engineering when seniors organized a workshop where security professionals demonstrated a live attack using the Metasploit Framework. They compromised one system with another and even changed the victim’s wallpaper remotely. Watching that happen in real time made everything click for me. Until then, I was mainly interested in networking and development, but that workshop showed me how those skills could be applied in security and sparked my interest in the field.
I was particularly drawn to the practical side of security, which led me to penetration testing. I started attending security sessions, exploring online resources, and participating in bug bounty programs. Over time, I began my professional career as a pentester while continuing bug bounty work. Later, through my friend Parveen Yadav, I learned about Cobalt and joined the platform, where collaborating with skilled professionals globally has further strengthened my approach to security testing.
What exploit or clever attack are you most proud of and why?
One engagement that stands out involved testing a subscription-based application with several security protections in place. The team shared two builds with us, a protected version and an older unprotected one. While reviewing the unprotected build and doing deeper reconnaissance, I discovered several hardcoded endpoints that were not visible in the live application.
One of those endpoints was related to a feature that was no longer available in the application interface but was still active on the backend. By interacting with that endpoint, I was able to upgrade a trial account to a premium plan without proper authorization checks. What made this memorable for me was that the issue came from careful recon and reviewing legacy functionality that had been overlooked.
What is your go-to brag when talking about your pentesting skills?
If I had to highlight one strength, it’s persistence in expanding the attack surface.
I rarely limit myself to what is exposed through the UI. I extract endpoints from JavaScript files, reverse engineer mobile applications, reconstruct hidden flows, read developer api docs, and test undocumented APIs.
My approach focuses on depth rather than surface coverage.
Can you share a time when something went wrong in the course of a pentest? What happened, and what did you do?
There was an assessment where the scope required focusing on access control testing, but only a basic user account was provided. Without elevated access, identifying role-based functionality becomes more challenging.
I searched for exposed references, analyzed archived content, and extracted every JavaScript resource I could access. By reconstructing API calls and experimenting with role parameters, I uncovered hidden administrative functionality that allowed user invitation and role manipulation.
It required additional effort, but the result was meaningful. The experience reinforced that constraints often push you toward better investigative techniques.
What are your favorite tools or TTPs when conducting pentests? Why do you find them effective?
For mobile testing, I rely heavily on JADX for Android analysis because it provides clarity into activities, classes, and logic. For iOS engagements, reverse engineering tools like Hopper assist with deeper inspection.
For web and API assessments, Burp Suite is central to my workflow. I use it alongside authorization testing extensions, Pentagrid Scan Controller to focus testing scope, and token management tools to maintain session stability.
However, tools are secondary to the process. My methodology typically involves static review, dynamic interaction, endpoint extraction, parameter manipulation, and business logic testing. Structured thinking is more important than any individual tool.
What are your favorite asset types (web applications, APIs, network, etc.) to pentest and why?
Mobile applications combined with APIs are particularly engaging for me. Mobile apps often interact with backend endpoints that do not receive the same scrutiny as traditional web applications. Testing for insecure WebView implementations, deep link handling issues, exported activity misconfigurations, and local authentication bypass scenarios often reveals significant findings.
The interplay between client behavior and backend logic creates a broader and more interesting attack surface.
What certifications do you have? Why did you go for those ones specifically?
I initially pursued the Mobile Application Penetration Tester (eMAPT) certification because that aligned with my strongest area of interest at the time. Later, I completed the advanced Web Application Penetration Tester eXtreme (eWPTX) to strengthen my exploitation skills across a broader range of attack vectors.
I also earned the Offensive Security Certified Professional+ (OSCP+) certification and Certified AI/ML Pentester (C-AI/MLPen) certification
What advice do you wish someone had given you when you first started pentesting?
When I first started pentesting, I wish someone had told me that it is not about speed. Early on, I spent a lot of time focusing on finding as many issues as possible. With experience, I realized that the real value of a penetration test comes from understanding how the application actually works. Looking closely at business logic, user workflows, and the purpose of the system often leads to more meaningful findings.
Before starting testing today, I spent time understanding the application architecture, authentication mechanisms, and areas that handle sensitive operations. Automated tools are useful for coverage, but manual testing and understanding the context of the application usually uncover the most impactful issues. I also learned that clear reporting is just as important as finding vulnerabilities, since the report often becomes the client’s long-term reference for improving their security posture.
How do you approach explaining findings to customers during a pentest? Is there a way you discuss your findings with customers? How do you ensure they have a quality experience?
When speaking with teams, I focus on root cause, reproduction steps, and remediation strategy. When presenting to leadership, I translate technical risk into business impact, explaining how vulnerabilities could affect data integrity, operational continuity, or reputation.
For example, when identifying an exposed administrative registration endpoint, I explained not only how it worked technically, but how it could allow unauthorized control of administrative workflows. Framing impact in practical terms helps ensure findings are understood and prioritized appropriately.
What is your favorite part of working with a pentesting team? What about working on your own?
Working within a team brings diverse thinking styles. Discussing blockers often leads to creative solutions that may not emerge individually. Collaboration accelerates discovery.
Working independently, however, allows uninterrupted focus and deeper exploration. Both environments are valuable, but I particularly appreciate the collaborative mindset where ideas and methodologies are openly exchanged.
Why do you like pentesting with Cobalt?
Cobalt provides exposure to a diverse group of highly skilled professionals across different regions. The environment encourages collaboration rather than competition, which creates opportunities to learn from different perspectives.
The structured engagement model and clear communication processes also support high-quality outcomes. It’s a platform that values depth and thoughtful testing.
Would you recommend Cobalt to someone looking for a pentest? Why or why not?
Yes, I would recommend Cobalt to organizations looking for a penetration test. Cobalt brings together experienced security professionals and a collaborative testing approach that helps deliver thorough and reliable assessments.
Their engagements focus on more than surface-level scanning. The testing process emphasizes depth, context, and clear communication, which allows organizations to receive thoughtful and actionable security insights.
What do customers or the media often misunderstand about pentesters?
A common misunderstanding is that pentesters simply rely on automated tools to exploit systems.
In reality, effective pentesting involves much more than running tools. It requires analytical thinking, a structured methodology, careful adherence to scope, and clear communication. While tools help with gathering information and identifying potential issues, discovering meaningful vulnerabilities often depends on understanding the application context and applying manual analysis.
How do you see pentesting changing in 2026 and over the next few years?
Applications are becoming more distributed, API-driven, and integrated with AI components. This expansion increases complexity and attack surface.
Future pentesters will need stronger cloud security understanding, deeper API analysis skills, and awareness of AI misuse risks. Automation will continue improving, but human judgment will remain central, especially for business logic and architectural flaws.
Adaptability will be essential.
What’s one non-technical skill (e.g., writing, communication, project management) that you believe is becoming critically important for a successful pentester, and how do you cultivate it?
A vulnerability has limited value if it is not clearly explained and actionable. I focus on writing reports that are structured, precise, and impact-oriented. During discussions, I aim to be concise and practical so that stakeholders understand not only the issue but why it matters and how to resolve it. Strong communication ensures findings translate into meaningful security improvements.
What's your p(Doom)?
Technology will continue evolving, including AI systems. However, the security community and broader research ecosystem adapt alongside technological change. In my view, the greater risk is complacency rather than innovation itself.
As long as practitioners continue to approach emerging technologies with critical thinking, continuous learning, and disciplined analysis, we will be better positioned to manage the risks that come with them.