The Responsible AI Imperative
Discover how to bridge the critical readiness gap as AI transitions into autonomous systems that don't just answer questions, but execute plans and interact with your digital environment independently.






Powered by over a decade of pentesting data, Cobalt combines intelligent automation with expert pentesters to uncover the vulnerabilities attackers actually exploit—faster and at scale.

Our AI-powered platform integrates continuous learning across the pentest by leveraging 10+ years’ of proprietary exploit intelligence. Insights from every pentest we’ve conducted drive unmatched automated reconnaissance, scanning, and triage. Because our AI handles rote tasks, our pentesters dedicate 100% of their energy to depth, using sophisticated adversarial tactics to identify high-impact vulnerabilities that pose the greatest risk to your business.

A decade of proprietary exploit data fuels our agents, ensuring every pentest learns from the last to make your entire security program smarter.
Autonomous agents execute the discovery phase at machine speed, ensuring our pentesters start testing with a complete understanding of the attack surface and focus exclusively on active exploitation.

Agents handle the noise so our experts focus on what machines cannot: chained exploitation, business logic abuse, and sophisticated adversarial scenarios. The result is deeper testing and more meaningful risk validation.
We’ve built an automated pipeline that mirrors the tactics of real-world attackers. By automating the initial stages of the attack chain—from reconnaissance to active scanning—we expose vulnerabilities exactly as a hacker would. This allows our elite experts to skip the baseline and focus entirely on complex exploitation, creative adversarial tactics, and business logic abuse - the vulnerabilities that represent real risk to your business.

AI maps your attack surface, discovering hidden APIs, subdomains, and externally exposed assets that attackers use as entry points.

Automated testing validates credentials and surface-level flaws to set an immediate risk baseline.

Findings are normalized and enriched with global threat intelligence feeds for real-world context. This intelligence is delivered directly to the pentesting team, accelerating the identification and validation of critical risks.

Our elite pentesters use this triage data as a baseline so that they can focus on advanced attack techniques:
The result is deeper testing and more meaningful risk validation.




Discover how to bridge the critical readiness gap as AI transitions into autonomous systems that don't just answer questions, but execute plans and interact with your digital environment independently.
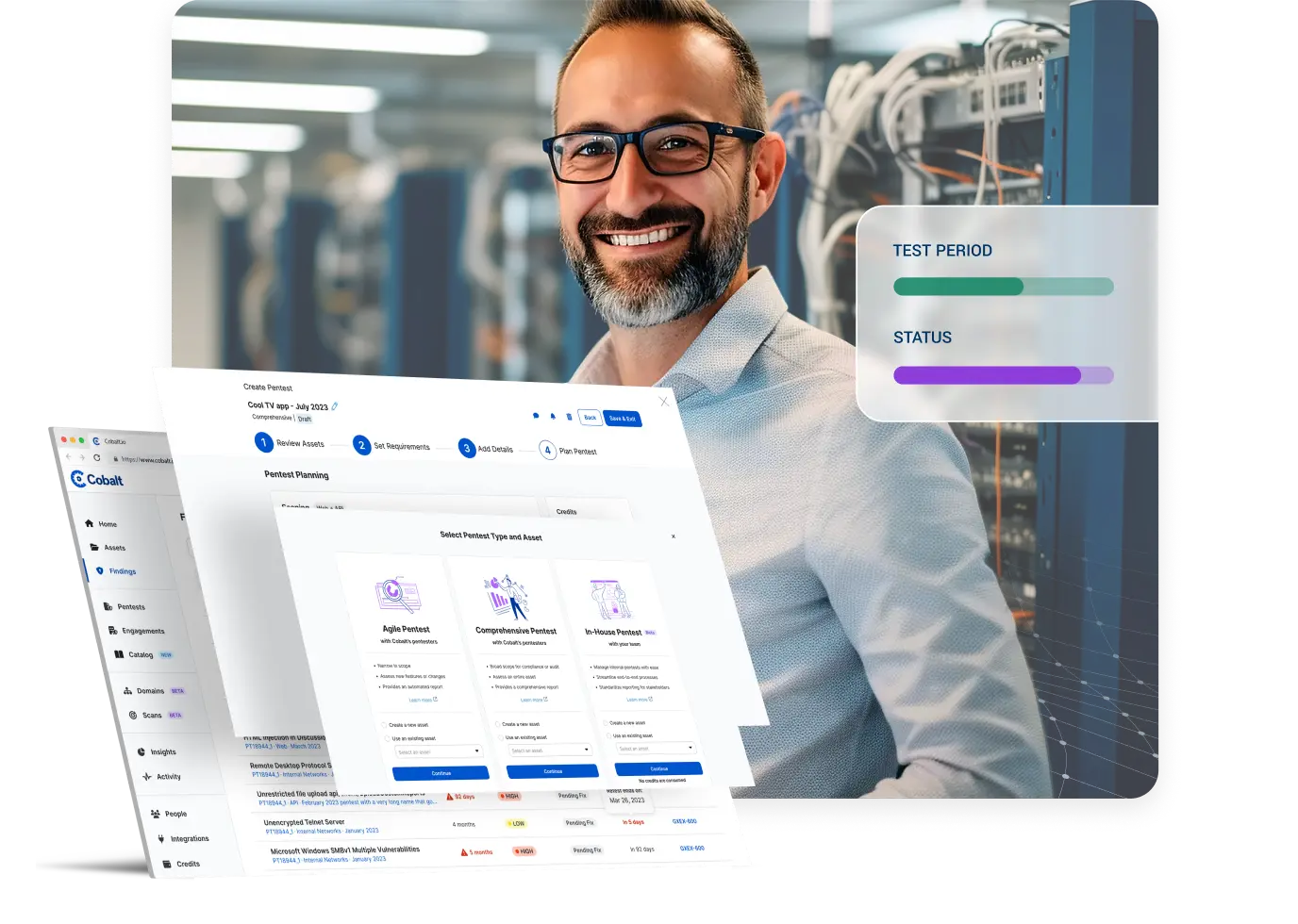
Our users consistently rely on Cobalt as the centralized, automated platform they need to solve complex security challenges. ...
I’m sure we’ve all heard some version of the same question: “Can we use AI for this? What about that?” The hype is everywhere. ...
Put a decade of proprietary exploit intelligence to work for your team. From easy scoping to AI-powered reporting, see how we’ve built the most efficient path from discovery to remediation.