State of Pentesting Report 2026
Discover key insights from the 2026 State of Pentesting Report, highlighting the critical gap in remediation practices and the importance of a programmatic approach to security.






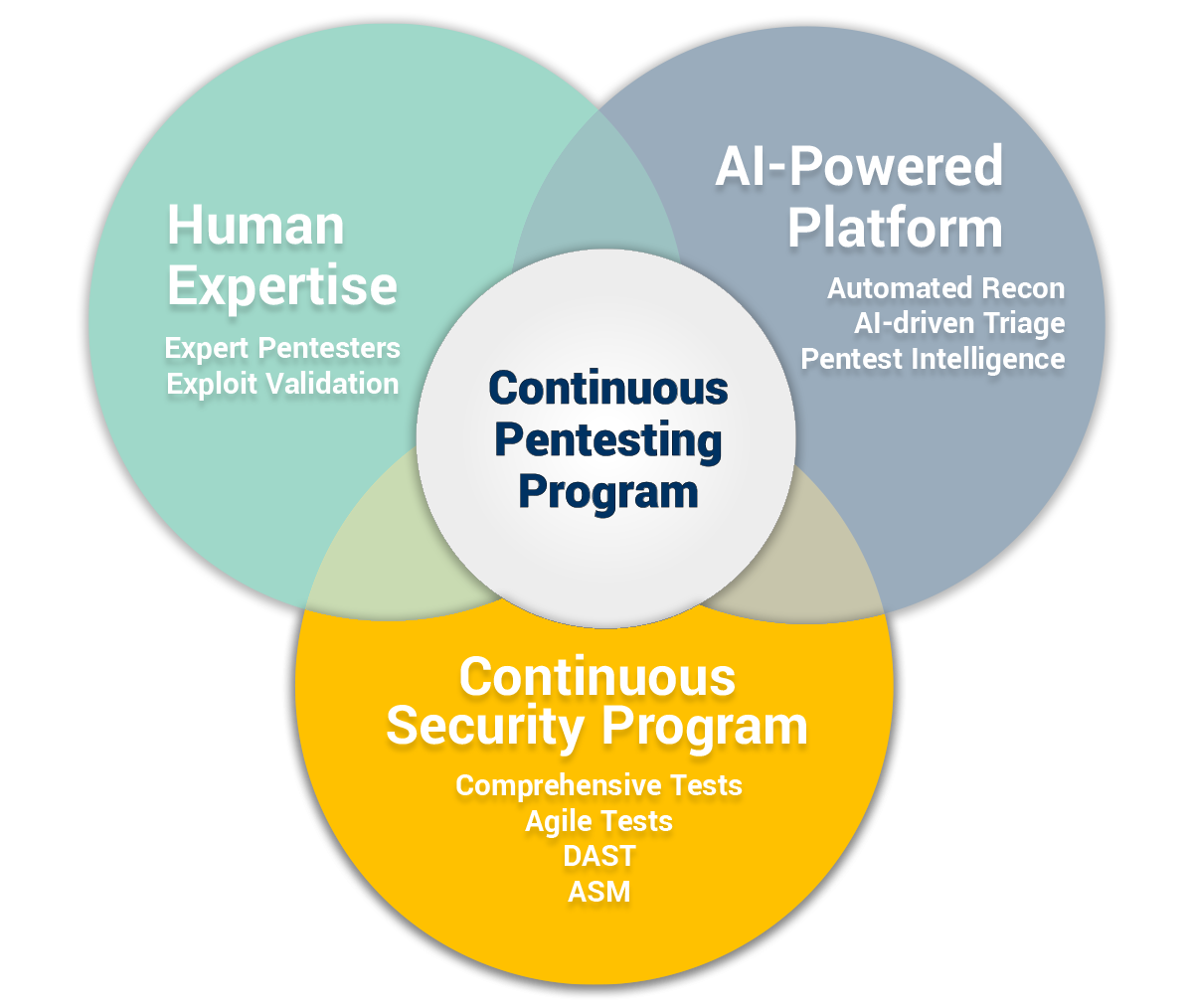
Move beyond point-in-time tests with a continuous pentesting program that combines expert human testing, AI-powered automation, and continuous monitoring to identify exploitable vulnerabilities across applications and infrastructure.
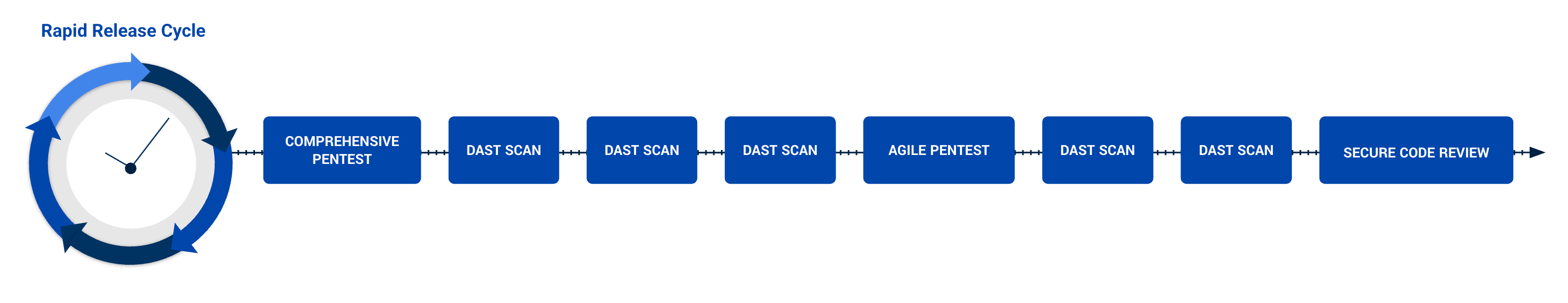
Traditional pentesting was designed for a slower world—one where applications changed infrequently, and infrastructure evolved gradually. Today, organizations deploy new code daily, APIs proliferate, and digital attack surfaces grow constantly.
Annual pentests alone can no longer keep pace.
Continuous pentesting provides a programmatic approach to offensive security that combines human-led testing, automated security validation, and continuous monitoring to identify exploitable vulnerabilities across your environment.
Find your weakest points, sharpen your incident response, and prevent data from being exposed




Traditional pentesting struggles to keep pace with modern development cycles. Cobalt delivers a programmatic approach to continuous pentesting that combines human expertise, AI-powered automation, and continuous monitoring to validate real-world risk across your applications and infrastructure.
Our approach integrates multiple testing methods into a continuous security program designed to evolve alongside your environment.
Our global community of vetted pentesters simulates real attackers to uncover vulnerabilities automated tools miss. Our experts focus on:
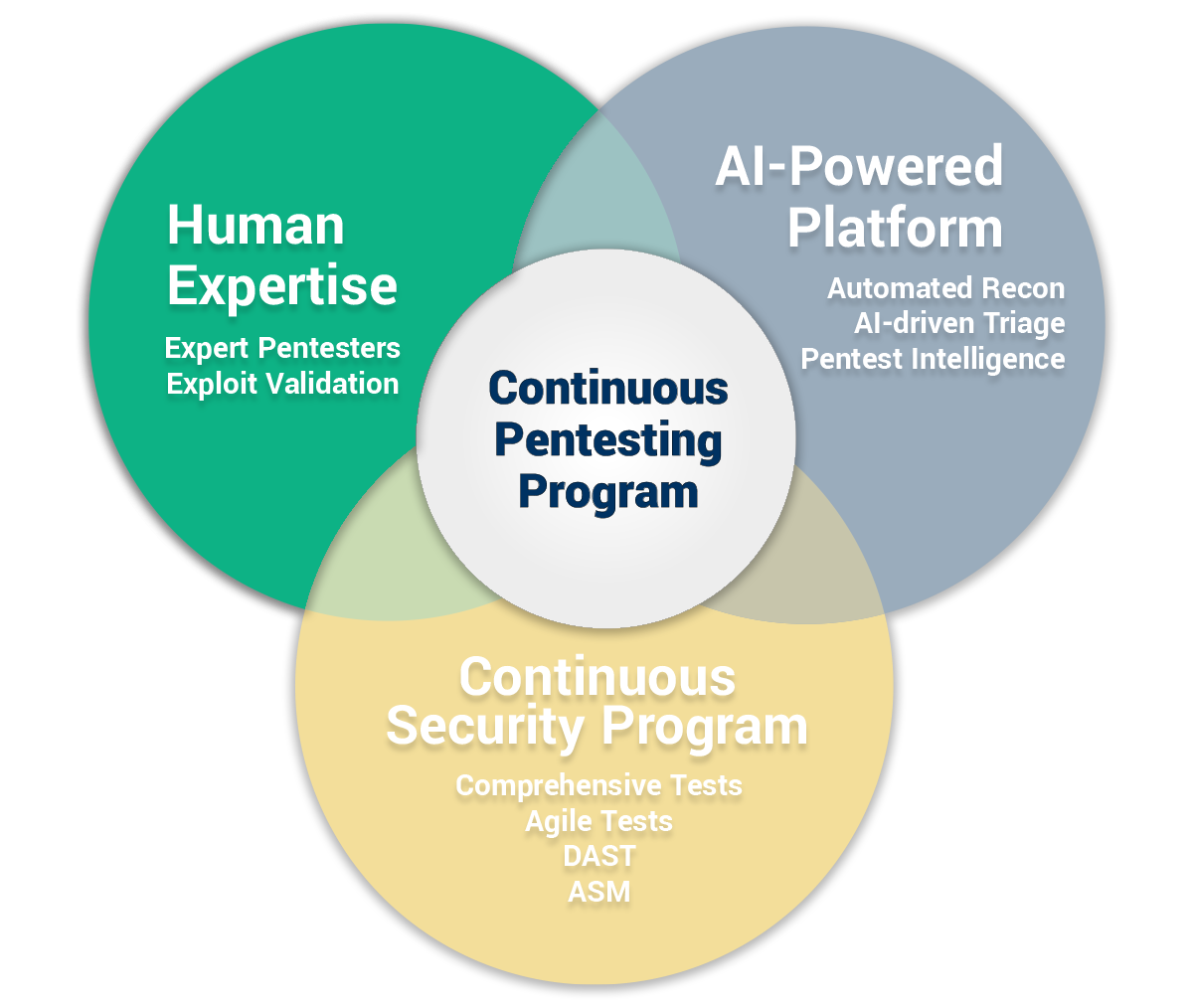
Cobalt’s platform uses AI to automate reconnaissance, scanning, and triage using insights from more than a decade of pentesting data.
This allows pentesters to spend 100% of their time on deep exploitation testing rather than manual setup.
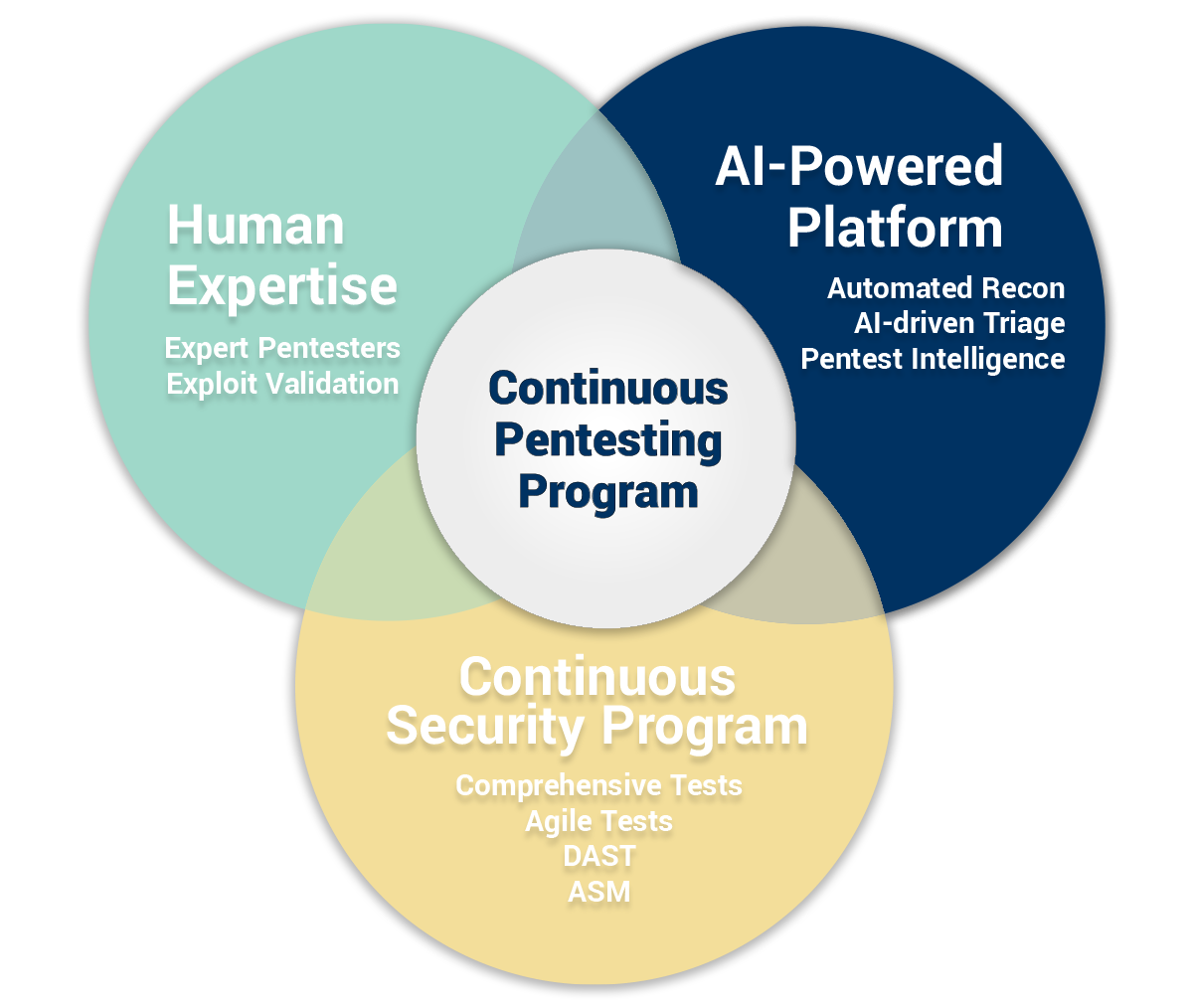
Continuous pentesting programs combine multiple services:
Security Program Managers coordinate testing across teams and assets to ensure testing aligns with development cycles.
Speed through automation. Scale through platform. Depth through human expertise.
We apply over a decade of security data to continuously learn, which makes our automation smarter and empowers our experts to conduct deeper, human-led pentesting at speed and scale.
We use an automated toolchain modeled after real-world attackers to map your attack surface and identify every potential entry point instantly.
Our AI-powered platform applies historical exploit intelligence to refine testing logic—ensuring every test is smarter than the last.
The best pentesters augmented with AI. Our experts focus on what machines cannot: business logic abuse and the creative attack scenarios of a sophisticated adversary.


"We reduced our annual testing costs by 44%—all while increasing our testing coverage. It was very easy to show the business the ROI."

"Cobalt has saved us 20% in costs in comparison to our top three previous vendors. And because of the automation and Jira integration, we're saving 50% of time in the overall scope of preparation, staging, and remediation for each pentest."

"Cobalt has redefined what it means to be a leader in offensive security. While many continuous solutions rely solely on AI and scripts, the human validation provided at Cobalt is the key differentiator. By leveraging Cobalt’s pentesting expertise, we move beyond the noise of raw data, allowing our team to focus on high-impact remediation rather than manual de-duplication."
Discover key insights from the 2026 State of Pentesting Report, highlighting the critical gap in remediation practices and the importance of a programmatic approach to security.
Learn what 10 years of pentesting data and a survey of 450 security leaders tells us about the AI security gap, why pentesting is more essential than ever, and much more.
Put a decade of proprietary exploit intelligence to work for your team. From easy scoping to AI-powered reporting, see how we’ve built the most efficient path from discovery to remediation.