XPath is a powerful language used to query and manipulate XML documents. It allows you to extract data, transform XML documents, query large datasets, and modify the structure and content of XML documents.
This power makes XPath a potential target for attackers looking to gain unauthorized access control of sensitive data through XPath injection attacks. By manipulating XPath statements, an attacker can compromise an entire system. Stay safe by guarding against XPath injection vulnerabilities in your applications.
Before moving to the XPath Injection, we will examine what XPath is.
XML Path Language - XPath
XPath is a language that allows you to navigate and manipulate the structure and content of XML documents.
XML is a popular format for storing and exchanging structured data and is often used in web development, data integration, and document management. With XPath, you can select specific elements or attributes within an XML document based on their tag name, attribute values, or position. It is commonly used in web development to extract and process data from XML documents or files.
import xml.etree.ElementTree as ET
# Parse the XML document
tree = ET.parse('document.xml')
# Find all elements with the tag 'item'
items = tree.findall('.//item')
# Print the text of each 'item' element
for item in items:
print(item.text)
This code will parse an XML document called 'document.xml' and find all elements with the tag 'item.' It will then print the text of each 'item' element. You can modify the XPath query to select different aspects or attributes in the XML document.
XPath Injection
Consider an application that allows users to search for articles in a news database that may be vulnerable to XPath injection attacks if it constructs XPath queries based on user input. The database for the application is stored in an XML document and uses XPath queries to search for articles based on various criteria, such as title, author, and publication date.
For example, if a user searches for articles published in 2020, the application may construct the following XPath query:
//article[publication_date='2020'].
However, if an attacker modifies the user input to include additional XPath statements, they may be able to manipulate the query to gain unauthorized access to sensitive data. For example, the attacker could enter the following search criteria:
2020' or '1'='1
This would modify the XPath query to the following:
//article[publication_date='2020' or '1'='1']
This modified query would return all articles in the database, bypassing the intended search criteria and potentially exposing sensitive information to the attacker. As a penetration tester, conducting security testing for XPath injection vulnerabilities in applications that use XPath queries to search or extract data from XML documents is essential.
Breakdown:
The XPath expression //article[publication_date='2020'] searches the articles element in an XML document for article elements with a date element with a value of 2020.
The part of the expression inside the square brackets, date=2020' or '1'='1, is known as a predicate. It specifies a condition that must be met for an element to be selected by the query. In this case, the predicate includes two conditions separated by the OR operator (or).
The first condition is date=2020', which checks for article elements with a year element equal to 2020. The single quote at the end of this condition is likely an error and would cause the XPath query to fail.
The second condition is '1'='1', which is always true because the two strings being compared are equal. This means that the OR operator will always evaluate to true, and all article elements will be selected by the query regardless of the value of the year element.
Blind XPath Injection:
In this attack, the attacker manipulates the XPath query in a way that does not produce any visible results but still allows them to retrieve sensitive data or modify the XML document. This type of attack is often more challenging to detect because there is no visible indication that the attack has occurred.
XPath Injection to Authentication Bypass:
XPath injection to authentication bypass is an attack involving injecting malicious code into an XPath query to exploit vulnerabilities in how an application constructs and processes XPath queries. This attack is often used to bypass authentication controls and gain unauthorized access to a web application or system that uses XPath queries to retrieve user credentials and grant access.
An example scenario of XPath injection being used to bypass authentication:
An attacker attempts to gain unauthorized access to a web application that uses an XML document to store user credentials. The XML document is structured as follows:
<users>
<user id="1">
<username>admin</username>
<password>password123</password>
</user>
<user id="2">
<username>user1</username>
<password>password456</password>
</user>
<user id="3">
<username>user2</username>
<password>password789</password>
</user>
</users>
The attacker notices that the login function of the application uses an XPath query to retrieve the user's credentials from the XML document and check if they are correct.
The attacker crafts the following malicious XPath query:
/users/user[username="admin" and password="' or '1'='1"]
The XPath query consists of two main parts: the path to the element being queried and the condition in the square brackets. In this case, the path /users/user specifies that the query is looking for user elements that are children of the user element. The condition [username="admin" and password="' or '1'='1"] specifies that the query is looking for user elements with the attribute username set to "admin" and the attribute password set to "' or '1'='1".
The condition in the square brackets is designed to constantly evaluate to true, regardless of the actual values of the username and password attributes. This is because the condition contains the string "' or '1'='1", a Boolean condition that will constantly evaluate to true. As a result, the query will return all user elements in the XML document, regardless of username and password values. Without any indication that the login has failed, the application will allow the attacker to access the application, even though they have not provided the correct credentials. This allows the attacker to bypass the authentication process and gain unauthorized access to the application.
Let's take a look at a practical demonstration of XPath injection to authentication bypass:
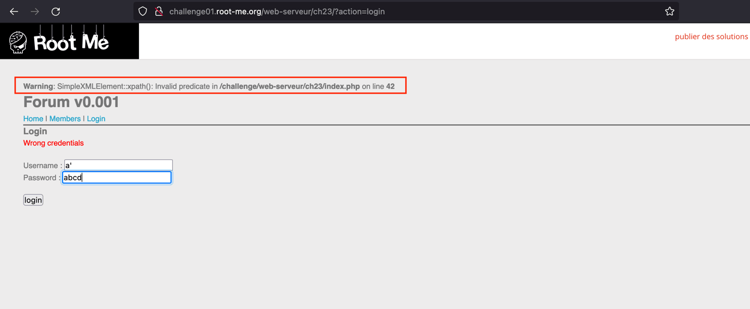
We will use the root-me.org lab to demonstrate this attack:
-
Navigate to the login page.
-
To check whether an XPath is present, insert a’ in the login field.
-
The error confirms that the XPath Injection is possible on the login page.
-
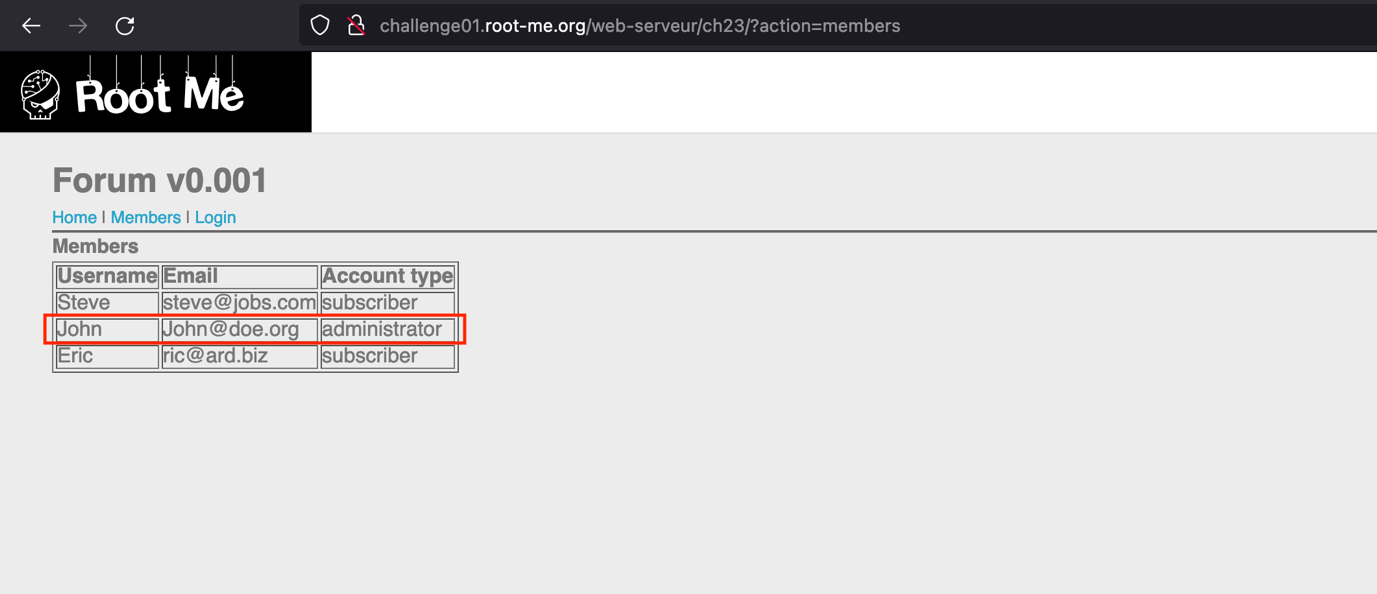
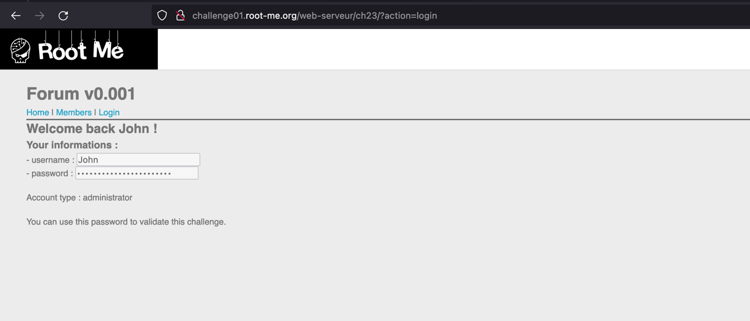
Navigate to the Members section, and note that John has an administrative account.
-
Insert the malicious payload in a username field to bypass the authentication.
John' or 'a'='a
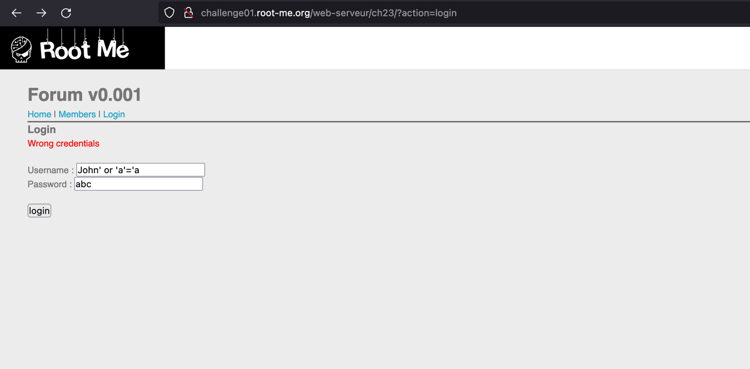
-
We have successfully exploited the XPath Injection to bypass authentication.
XPATH injection attacks can have serious consequences, allowing attackers to access sensitive data and potentially compromise an entire system. However, several measures can be taken to prevent XPath injection attacks.
Remediations
1. Sanitize User Input
It is important to properly sanitize all user input before using it in an XPath query. This includes validating and filtering the input to ensure it does not contain malicious code or characters.
2. Use Parameterized XPath Statements
Parameterized XPath statements allow you to specify placeholders for user input rather than including the input directly in the query. This helps to prevent attackers from injecting malicious code into the query.
3. Implement Proper Error Handling
Proper handling can help prevent attackers from using error messages to gather information about the application or the system it runs on.