About Pentesting
Pentesting, or penetration testing, is a security assessment with the goal to improve security by discovering exploitable vulnerabilities in security defenses. It provides an in-depth analysis of a series of simulated attacks on an application or network to check its security posture.
The main drivers for pentesting include the struggles to fix and prevent common vulnerabilities, a growing need for compliance, and the impact and severity of security attacks — to name a few.
“Organizations hire penetration testers to review specific parts of an application, sometimes taking a broad look across an application or digging down into specific features and functionality. These types of tests can be especially useful for providing depth of coverage for applications that require specialized knowledge to test effectively…” A Manager’s Guide to Selecting the Best Testing Approach for Your Application Security Needs
Pentest Phases
The structure of a pentest program includes a series of phases outlined:
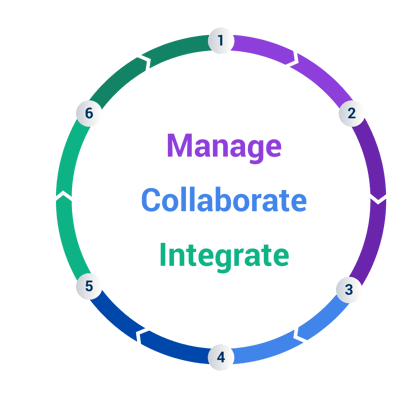
- Discover. Mapping out your attack surface gives you a clear vision of your applications, APIs, networks, cloud instances, and other assets you might be managing.
- Plan. Make a decision on which security testing partner you’ll work with and how the testing will be structured.
- Test. The customer meets the testing team, and it’s time for testing to begin.
- Remediate. A report of each vulnerability is provided in real-time, enabling teams to start working on fixes and remediation.
- Report. The vendor provides a test report listing all discovered vulnerabilities, participating pentesters, used methodologies, and the actions you’ve taken during “Remediation.”
- Analyze. It’s important in this final step to take the documentation and draw actionable insights from it.
When is penetration testing most effective?
It’s important to know your vulnerabilities and how attackers might exploit them. First, take inventory of all of your assets (websites, digital infographics, servers, etc.) to set a clear scope and plan for exposure detection.
When teams are aligned on the details, scope, and preparation, it leads to a more effective testing process with more coverage and better results. It’s essential that vulnerabilities are tested and retested over time to ensure fixes are effective. Pentesting is most effective when assets are most vulnerable — before an attack occurs.
Here are some quick best practices to prepare for a pentest:
- Align security and development teams
- Focus on the scope
- Work with the right partners for proactive cybersecurity
After a pentest is complete, “Pentesting requires companies to do more than simply receive a report at the end of the test. The true value derived from a pentest is through the remediation of discovered vulnerabilities. Without taking action from your pentest results, there’s a missed opportunity to capture the full value from pentesting. It’s vital for standard pentest results interpretation to include a remediation plan.” — Generating Actionable Pentest Results with PtaaS.
Pentesting isn’t a “one and done” technique — assets require regular testing, at least once a year to ensure valuable results. Typically, programs run on a rolling annual basis, with some companies completing tests at monthly or quarterly intervals.
Looking for better security with effective pentesting?
Explore other types of security testing, including penetration testing services offered by Cobalt.