Man-in-the-middle (MITM) attacks are on the rise, and it’s easy to see why. People download more apps and software on their phones than ever. This provides an easy gateway for cybercriminals to gain access to your information.
MITM attacks are any attack where threat actor(s) place themselves in the middle of a user and an application, similar to an eavesdropper listening in on a private conversation. The user feels comfortable providing sensitive information because they believe they are communicating only within a trusted platform, not realizing there is a malicious spy on the other end.
According to IBM’s X-Force Threat Intelligence Index, 35% of all exploitation activity involves MITM attacks. It’s important for organizations to remain aware of new developments in MITM attacks and how to identify them to protect their employees, clients, and vendors.
As of 2023, it’s estimated that cybercriminals attempt a cyberattack every 39 seconds. The most common MITM attacks are Internet Protocol (IP) spoofing, Domain Name System (DNS) spoofing, and Hypertext Transfer Protocol (HTTP) spoofing. This article covers the steps cybercriminals commonly take to execute these kinds of attacks. Hopefully, this helps you understand the anatomy of the vulnerabilities in your software that have the potential to be exploited.
IP Spoofing
Internet Protocol (IP) spoofing refers to the act of hiding the source of IP packets, making it difficult to discern their true origin. The hacker creates their own IP packets, which are then used to change the source IP address to impersonate a trusted entity or disguise the sender’s true location.
Internet traffic is sent in units known as packets, containing routing information via IP headers. These IP headers include the source IP address and destination address, much like a letter in the mail contains a delivery address and a return address. Ensuring that these addresses are accurate is important in protecting from attacks commonly used in bank fraud and other financial scams, for example.
How is IP spoofing done?
The hacker first changes the source address in the outgoing packet header in a way that causes the destination computer to perceive this packet as coming from a trusted source. Once identified as such, the computer or platform accepts the packets.
A cybercriminal then continuously randomizes the source address using a specific tool to create a fake packet header. Another method they may use involves using the IP address of another device so that any input is received by the spoofed packet instead of the proper destination.
Attackers need access to some vital information before carrying out an IP spoofing attack. First, a cybercriminal needs to identify a trusted IP address that the targeted device would identify as legitimate and allow it to penetrate the network.
Unfortunately, obtaining device IPs is extremely simple. There are ample online databases of IP address-to-device mappings used for ethical hacking and other legitimate purposes, but also frequently employed by malicious hackers in their plotting.
The second requirement for IP spoofing is a little more difficult to obtain. Hackers must have the ability to intercept the legitimate packet and then swap out the real IP header for a spoofed one. Hackers generally use Address Resolution Protocol (ARP) scans or a networking sniffing tool to aid them in hijacking network packets.
The security risks of IP spoofing
IP spoofing helps bad actors gather data on users that can be used to hack into accounts or, more commonly, sell user data on the dark web to hacking organizations, many of which are state-sponsored by governments worldwide. These attacks are a huge concern for financial institutions, where the reward can be high for gaining access to networks. Consumers should look to do business with banks that offer security features such as biometric logins as a means to mitigate this risk.
IP spoofing can also be used as an effective tool in Distributed Denial of Service (DDoS) attacks, in which the hacker disguises their fake requests to bombard a network with traffic to slow down servers.
How to detect IP spoofing
Naturally, it is difficult for users to detect when IP spoofing is happening — that’s the whole point and the reason behind its efficacy. However, ethical hackers and cybersecurity professionals can and should be able to detect when IP spoofing occurs within their organizations.
This requires constant surveillance of the network layer or Layer 3 of the Open Systems Interconnection communications model. Organizations can use network monitoring tools to perform traffic analysis at network endpoints. One of the most common ways of doing this is through packet filters, which are commonly contained in routers and firewalls.
These packet filters can notify cybersecurity professionals of inconsistencies between the packet’s IP address. This tool identifies both legitimate IP addresses on access control lists (ACLs), as well as fraudulent packets so attacks can potentially be stopped in their tracks.
Packet filtering is performed via ingress or egress filtering, ideally used in unison. As their name implies, ingress filters analyze packets that a network is receiving to see if the IP header is legitimate. It will filter out any that are suspicious or unidentified on the ACL. Egress filters are similar in that they monitor outgoing source IP addresses that don’t match the organization’s network. This is effective in preventing insider hacking, a growing concern involving those with inside access to your systems using this privilege to launch an attack.
Like nearly all cybersecurity vulnerabilities, there is no way to prevent IP spoofing completely. The key to handling this threat is through early intervention and maintaining heightened protection for your network, which makes IP spoofing attacks difficult to carry out.
Another way that organizations can prevent IP spoofing is by using strong authentication procedures that don’t rely on IP address verification alone. Antivirus software that watches for suspicious activity can be used in unison with packet filtering to stop attacks in their tracks. IP encryption can protect ingoing and outgoing traffic from your network and make IP spoofing attacks much harder to launch.
Finally, your organization should always keep your network updated with the latest patch updates to avoid identified vulnerabilities from being exploited.
DNS Spoofing
Domain Name System (DNS) spoofing or DNS cache poisoning is used to redirect a user seeking out a legitimate domain to a bogus domain. Once redirected, the fraudulent website captures usernames, passwords, and other sensitive information.
How is DNS spoofing done?
A MITM attack uses DNS spoofing to dupe both a company and a client into thinking the IP address they are communicating with is legitimate when it is really the same IP address on both sides, connected to the hacker’s network.
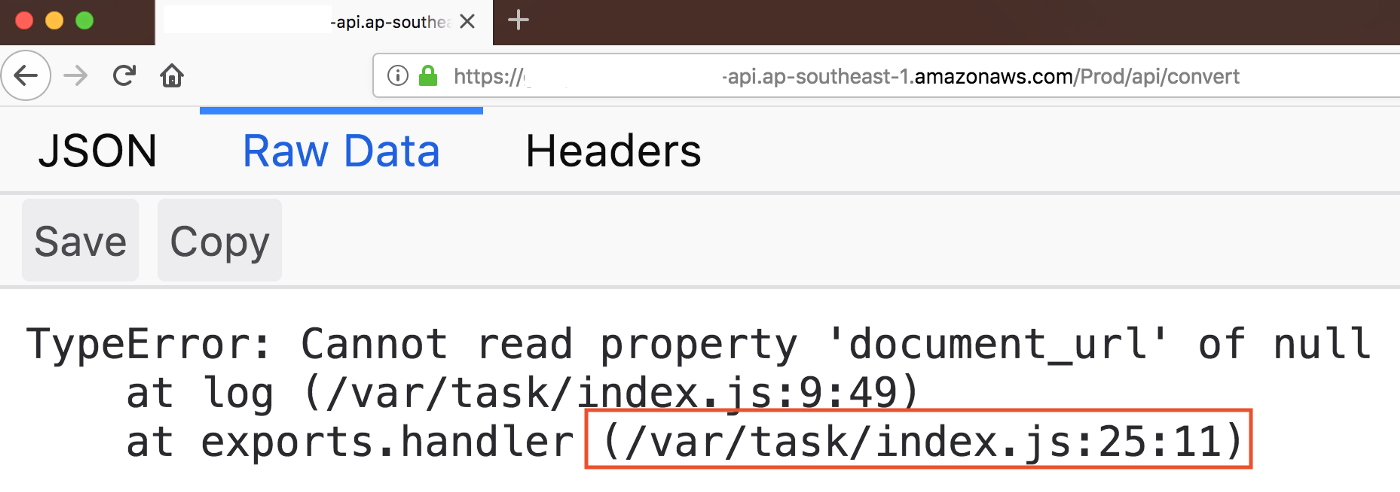
For example, the aspiring cybercriminal employs a tool such as arpspoof to create a command which modifies the MAC address in the server’s ARP table, opening the door that will allow them to proceed with their attack.
By issuing the Linux command “echo 1> /proc/sys/net/ipv4/ip_forward,” the IP packets sent between the client and company are redirected to the hacker’s own network. The host file on the attacker’s network then maps the legitimate website to its own local IP, creating a fake website that resembles the legitimate one.
A tool such as dnsspoof then is used to capture all DNS requests and send them straight to the hacker, gathering information or being used to install ransomware, malware, or spyware on the user’s computer.
How to prevent DNS spoofing
DNS is unencrypted, and DNS servers do not validate the IP addresses they direct. Your organization can use domain name server security (DNSSEC) tools to provide additional verification methods to prevent this type of attack.
DNS filtering and the regular application of patching can also help prevent DNS spoofing attacks in much the same way they prevent IP spoofing attacks. Lastly, clients, vendors, and employees should be encouraged to pay attention to the secure connection symbol shown as a padlock near the address of any website they access.
HTTP Spoofing
Noticing the secure connection symbolized by a padlock next to the website’s address is a great way to prevent your computer from being compromised by DNS attacks. However, HTTP spoofing is another MITM attack that can be utilized even within a secure connection. According to recent research, 43% of all banking employees from large firms are likely to fall victim to a convincing phishing attack, many of which rely on fake HTTP addresses.
This method of attack is much less technical than IP or DNS spoofing but no less harmful. In this type of attack, hackers create a website nearly identical to a legitimate website, targeting those who make a mistake when typing in the correct website address. Less commonly known as a “homograph attack,” the characters in the target domain are replaced with similar non-ASCII characters.
These websites are commonly used in phishing attacks, where hackers send emails or texts to users with links to these nearly identical sites. Most browsers support Punycode hostnames in their address bars, making it difficult to determine that the website is illegitimate.
Organizations are limited in their ability to protect themselves from these attacks. However, they can proactively search for websites with similar addresses and report fake ones to the Internet Crime Complaint Center (IC3).
Cybercriminals look to take advantage of vulnerabilities they identify on either end of internet transactions. MITM attacks are on the rise, and it is important for organizations to stay vigilant to protect their customers, employees, and vendors.